MITRE ATT&CK T1086 PowerShell
- The Tech Platform
- Oct 1, 2020
- 4 min read
Our research has found that PowerShell was the second most prevalent MITRE ATT&CK technique used by adversaries in their malware. PowerShell is a powerful interactive command-line shell and scripting language installed by default on Windows operating systems. Since PowerShell has extensive access to Windows internals, system administrators frequently use it to manage and configure the operating system, and automate complex tasks.
Not only system administrators, but also adversaries have realized the potential in incorporating such a powerful tool into their arsenal. Hence the reason, PowerShell appeared as the second most frequently used MITRE ATT&CK technique in our research.
The purpose of this blog post is to review:
the fundamentals of the PowerShell technique,
why and how adversaries use PowerShell,
which threat actors and malware use the technique, and
red, blue, and purple teaming exercises for the PowerShell technique.
Introduction
It is easy to detect a third-party program that is used to execute commands on Windows OS. Therefore, adversaries frequently use built-in Windows command-line and scripting tools to run their commands. PowerShell is one of those tools that enable attackers to:
On this account, the technique provides three significant benefits for adversaries:
create fileless malware that runs in the memory without leaving any traces on disk
perform sophisticated actions with extensive access to OS internals
persist on the system by regularly loading malicious code into memory
discover information, collect and exfiltrate data
move laterally through networks
Although the PowerShell technique is categorized only in the Execution tactic of the MITRE ATT&CK framework, it is also a powerful technique to achieve the Defense Evasion tactic. Adversaries use PowerShell to employ the following defense evasion techniques:
direct, in-memory loading and execution of malicious code
downloading and executing malware payloads without writing any data to disk (fileless execution)
executing complex code without installing additional software (T1064 Scripting)
evading Antimalware Scan Interface (AMSI) and changing Windows Defender settings (T1089 Disabling Security Tools)
blocking events by disabling Script Block Logging (T1054 Indicator Blocking)
injecting malicious code into legitimate processes (T1055 Process Injection)
locating and impersonating user logon tokens (T1134 Access Token Manipulation)
How do threat actors leverage publicly available PowerShell tools?
Extensive capabilities of PowerShell have attracted the attention of red teams and penetration testers. Consequently, powerful red team and penetration testing frameworks and tools have been developed using PowerShell, such as Empire (PowerShell Empire) [1], PowerSploit [2], Nishang [3], PoschC2 [4], and Posh-SecMod [5].
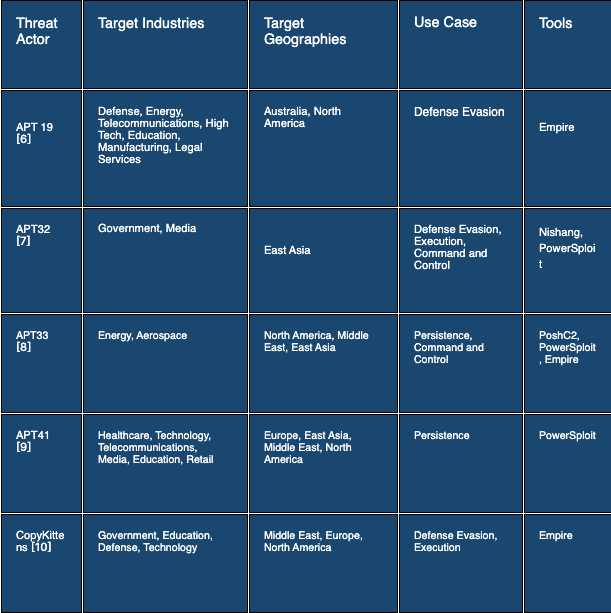
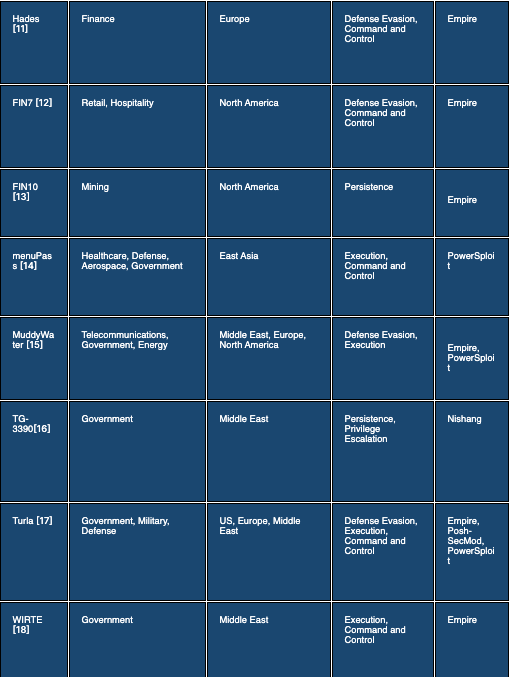
All of these tools are open source and publicly available. Although these tools are developed with the intention of using red teams and penetration testers, threat actors frequently leverage them for malicious purposes in cyber incidents. The following table presents some use cases of these PowerShell post-exploitation frameworks by threat actors.
Example: Getting Network Configuration Discovery via PowerShell
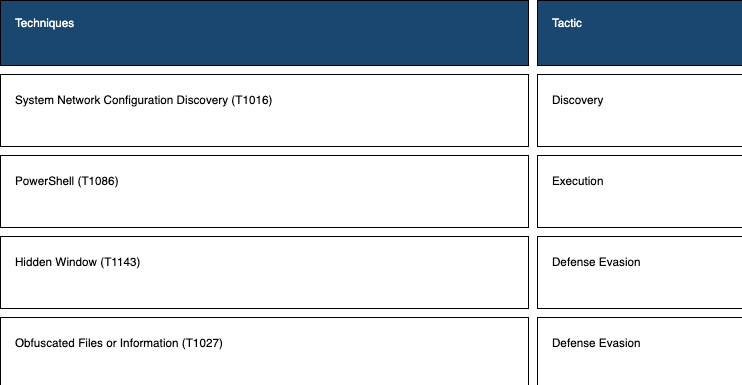
This section presents a simple PowerShell command that simulates the following techniques.
Read Teaming - How to simulate?
Briefly, the following PowerShell one-liner gets IP configuration properties using an encoded command.
PowerShell -w hidden -en RwBlAHQALQBOAGUAdABJAFAAQwBvAG4AZgBpAGcAdQByAGEAdABpAG8AbgA=Let’s split and analyse the command:
-w parameter: there is no parameter named -w according to the official PowerShell documentation [19]. In fact, the -w parameter is completed by PowerShell as the -WindowStyle parameter because of the parameter substring completion feature of PowerShell . PowerShell Parameter Completion: Substrings of parameters like -NoEx (- NoExit), -Executi (-ExecutionPolicy), -w (-WindowStyle) are used in the PowerShell command instead of using the complete parameter string to avoid detection. Because of the way that PowerShell handles parameters, parameter substrings like -W, -Wi, -WindowSt, -WindowSty, are all valid ways of specifying an execution argument such as -WindowStyle. -w can be used for -WindowStyle , because -WindowStyle is the only parameter that starts with -w.
-hidden value: Adversaries commonly use the -WindowStyle parameter with Hidden value in malicious PowerShell commands to avoid detection (T1143 Hidden Window). Actually, -WindowStyle Hidden does not entirely hide the PowerShell command windows, it shows the command window for a while before hiding it [19].
-en parameter: Similar to -w , there is not a parameter named -en according to the official PowerShell documentation [19]. The -en parameter is completed as -EncodedCommand parameter by PowerShell. -EncodedCommand accepts a base-64-encoded string version of a command [19].
RwBlAHQALQBOAGUAdABJAFAAQwBvAG4AZgBpAGcAdQByAGEAdABpAG8AbgA= value: this string is the value of the -EncodedCommand parameter. Therefore, we must use base64 decoding to reveal the PowerShell command (T1027 Obfuscated Files or Information). This string is the base64 encoded version of the following command: Get-NetIPConfiguration. Get-NetIPConfiguration: This PowerShell cmdlet gets IP configuration properties for all non-virtual connected interfaces on a computer(T1016 System Network Configuration Discovery) [20].
Blue Teaming - How to detect?
Sigma Rule
To detect network configuration discovery via Get-NetIPConfiguration cmdlet,
title: Network Configuration Discovery via PowerShell Cmdlet
status: experimental
description: Detects the attempt to obtain network configuration via Get-NetIPConfiguration cmdlet of PowerShell. This technique is commonly utilized for discovery.
author: Picus Security
references:
- https://attack.mitre.org/techniques/T1016/
- https://attack.mitre.org/tactics/TA0007/
- https://docs.microsoft.com/en-us/windows-server/administration/windows-commands/powershell
- https://docs.microsoft.com/en-us/powershell/module/nettcpip/get-netipconfiguration?view=win10-ps
logsource:
product: windows
service: security
definition1: 'Requirements: Group Policy : Computer Configuration\Windows Settings\Security Settings\Advanced Audit Policy Configuration\Audit Policies\Detailed Tracking\Audit Process Creation'
definition2: 'Requirements: Group Policy : Computer Configuration\ Administrative Templates\ System\ Audit Process Creation\ Include Command Line'
detection:
selection:
EventID: 4688
NewProcessName: '*\powershell.exe'
ProcessCommandLine: '*Get-NetIPConfiguration*'
condition: selection
falsepositives:
- Legitimate administrative activities
level: low
tags:
- attack.discovery
- attack.t1016
- attack.ta0007Appendixes
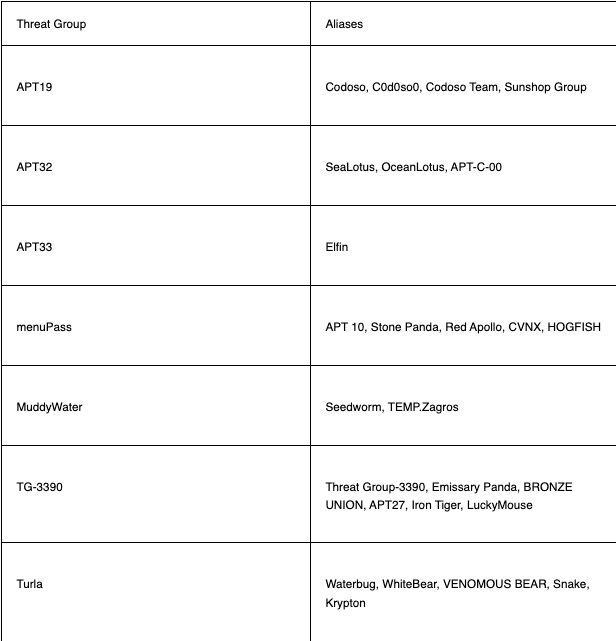
Appendix A - Aliases of Threat Groups
Source: pycus