What is phishing? Everything you need to know to protect yourself from scam emails and more
- The Tech Platform

- Aug 24, 2020
- 17 min read
Don't click on that email! Find everything you need to know in this phishing guide including how to protect yourself from one of the most common forms of cyber attack.
What is phishing?
Phishing is one of the easiest forms of cyber attack for a criminal to carry out, but one which can provide these crooks with everything they need to infiltrate every aspect of their targets' personal and working lives.
Usually carried out over email - although the scam has now spread to social media, messaging services and apps - a basic phishing attack attempts to trick the target into doing what the scammer wants. That might be handing over passwords to make it easier to hack a company, or altering bank details so that payments go to fraudsters instead of the correct account.
The aim and the precise mechanics of the scams vary: victims might be tricked into a clicking a link through to a fake webpage with the aim of persuading them user to enter personal information - it's estimated that an average of 1.4 million of these websites are created every month.
Other campaigns involve tricking users into downloading and installing malware - for stealthy approach to theft - or inadvertently installing ransomware, providing the attacker with much more immediate profit.
More complex phishing schemes can involve a long game, with hackers using fake social media profiles, emails and more to build up a rapport with the victim over months or even years in cases where specific individuals are targeted for specific data which they would only ever hand over to people they trusted.
That data can be as simple as an email address and password, to financial data such as credit card details or online banking credentials or even personal data such as date of birth, address and a social security number.
In the hands of hackers, all of that can be used to carry out fraud, be it identity theft or using stolen data to buy things or even selling people's private information on the dark web. In some cases, it's done for blackmail or to embarrass the victim.
In other cases, phishing is one of the tools used for espionage or by state-backed hacking groups to spy on opponents and organisations of interest.
And anyone can be a victim, ranging from the Democratic National Committee, to critical infrastructure, to commercial businesses and even individuals.
The spectre of a phishing attack against the Democratic National Committee loomed large over Hillary Clinton's Presidential campaign.
Image: iStock
Whatever the ultimate goal of the attack, phishing revolves around scammers tricking users into giving up data or access to systems in the mistaken belief they are dealing with someone they know or trust.
How does a phishing attack work?
A basic phishing attack attempts to trick a user into entering personal details or other confidential information, and email is the most common method of performing these attacks.
The sheer number of emails sent every single day means that it's an obvious attack vector for cyber criminals. It's estimated that 3.7 billion people send around 269 billion emails every single day.
Researchers at Symantec suggest that almost one in every 2,000 of these emails is a phishing email, meaning around 135 million phishing attacks are attempted every day.
Most people simply don't have the time to carefully analyse every message which lands in their inbox - and it's this which phishers look to exploit in a number of ways.
Scams vary in their targets - some are aiming at unwary consumers. Here, their email subject line will be designed to catch the victim's eye - common phishing campaign techniques include offers of prizes won in fake competitions such as lotteries or contests by retailers offering a 'winning voucher'.
In this example, in order to 'win' the prize, the victims are asked to enter their details such as name, date of birth, address and bank details in order to claim. Obviously, there's no prize and all they've done is put their personal details into the hands of hackers.
If that email 'prize' seems too good to be true, it usually is and it's usually a phishing scam.
Image: iStock
Similar techniques are used in other scams in which attackers claim to be from banks looking to verify details, online shops attempting to verify non-existent purchases or sometimes -- even more cheekily -- attackers will claim to be from tech security companies and that they need access to information in order to keep their customers safe.
Other scams, usually more sophisticated, aim at business users. Here attackers might also pose as someone from within the same organisation or one of its suppliers and will ask you to download an attachment which they claim contains information about a contract or deal.
In many cases the file will unleash malicious software onto the system - in many cases it will harvest personal data, but it in many cases it's also used to deploy ransomware or rope systems into a botnet.
Attackers will often use high-profile events as a lure in order to reach their end goals. For example, a major campaign used the lure of the 2016 Olympic Games to help distribute malware in the run up to the event.
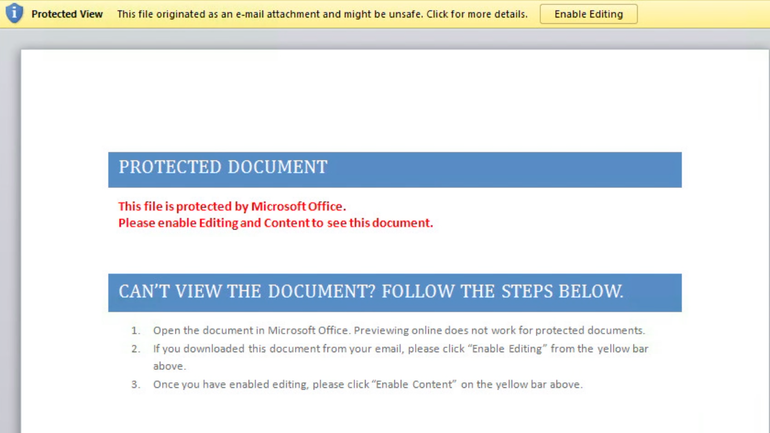
In many cases the malicious payload will be hidden inside a Microsoft Office document which requires the user to enable macros to run. The payload will trick the victim into enabling them by claiming that an update needs to be installed or permissions need to be given to allow the document to be viewed properly. But if users allows the payload to run they and their company are likely to be in big trouble.
Why is phishing called phishing?
The overall term for these scams -- phishing -- is a modified version of 'fishing' except in this instance the fisherman is the cyber attacker and they're trying to catch you and reel you in with their sneaky email lure.
It's also likely a reference to hacker history: some of the earliest hackers were known as 'phreaks' or 'phreakers'.
When did phishing begin?
The consensus is the first example of the word phishing occurred in the mid-1990s with the use of software tools like AOHell which attempted to steal AOL user names and passwords.
These early attacks were successful because it was a new type of attack, something users hadn't seen before. AOL provided warnings to users about the risks, but phishing remained successful and it's still here over 20 years on. In many ways, it has remained very much the same for one simple reason - because it works.
How did phishing evolve?
While the fundamental concept of phishing hasn't changed much, there have been tweaks and experimentations across two decades as technology and how we access the internet has changed. Following the initial AOL attacks, email became the most appealing attack vector for phishing scams as home internet use took off and a personal email address started to become more common.
Many early phishing scams came with tell-tale signs that they were not legitimate - including strange spelling, weird formatting, low-res images and messages which often didn't make complete sense.
Nonetheless, in the early days of the internet, people knew even less about potential threats which meant that these attacks still found success - many of these are still effective.
Some phishing campaigns remain really, really obvious to spot - like the prince who wants to leave his fortune to you, his one long lost relative, but others have become to be so advanced that it's virtually impossible to tell them apart from authentic messages. Some might even look like they come from your friends, family, colleagues or even your boss.
What's the cost of phishing attacks?
It's hard to put a total cost on the fraud that flows from phishing scams, but earlier this year the FBI suggested that the impact of such scams could be costing US business somewhere around $5bn a year, with thousands of companies hit by scams every year.
One example of a high profile incident: in July 2017 MacEwan University in Edmonton, Alberta, Canada fell victim to a phishing attack.
"A series of fraudulent emails convinced university staff to change electronic banking information for one of the university's major vendors. The fraud resulted in the transfer of $11.8 million to a bank account that staff believed belonged to the vendor," the university said in a statement.
What types of phishing scams are there?
The 'spray and pray' is the least sophisticated type of phishing attack, whereby basic, generic messages are mass-mailed to millions of users. These are the 'URGENT message from your bank' and 'You've won the lottery' messages which look to panic victims into making an error -- or blind them with greed.
Schemes of this sort are so basic that there's often not even a fake webpage involved - victims are often just told to respond to the attacker via email. Sometimes emails might play on the pure curiosity of the victim, simply appearing as blank message with a malicious attachment to download.
This is the way Locky ransomware was spread and was one of the the most effective forms of the file-encrypting malware around. More recently, this tactic has been used to spread GandCrab - one of 2018's most prolific forms of ransomware.
A simple Locky distribution phishing email - it looks basic, but if it didn't work, attackers wouldn't be using it.
Image: AppRiver
These attacks are mostly ineffective, but the sheer number of messages being sent out means that there will be people who fall for the scam and inadvertently send details to cyber attackers who'll exploit the information in any way they can.
What is spear phishing?
Spear phishing is more advanced than a regular phishing message and aims at specific groups or even particular individuals. Instead of vague messages being sent, criminals design them to target anything from a specific organisation, to a department within that organisation or even an individual in order to ensure the greatest chance that the email is read and the scam is fallen for.
It's these sorts of specially crafted messages which have often been the entry point for a number of high profile cyber attacks and hacking incidents and nation-state backed attackers continue to use this as means of beginning espionage campaigns
At a consumer level, it can be designed to look like an update from your bank, it could say you've ordered something online, it could relate to any one of your online accounts. Hackers have even been known to seek out victims of data breaches and pose as security professionals warning victims of compromise - and that targets should ensure their account is still secure by entering their account details into this handy link.
While spear phishing does target consumers and individual internet users, it's much more effective for cyber criminals to use it as a means of infiltrating the network of a target organisation.
Lure document used in a ransomware attack against a hospital - attackers used official logos and names to make the email and the attachment look legitimate.
Image: Proofpoint
This particular type of phishing message can come in a number of forms including a false customer query, a false invoice from a contractor or partner company, a false request to look at a document from a colleague, or even in some cases, a message which looks as if it comes directly from the CEO or another executive.
Rather than being a random message, the idea is to make it look as if it has come from a trusted source, and coax the target into either installing malware or handing over confidential credentials or information. These scams take more effort but there's a bigger potential payback for crooks too.
Hackers have also been known to hijack legitimate business email communications then use highly-customised phishing messages designed to look as if the victim is still communicating with the person they were originally messaging.
By hijacking legitimate conversations, and specially crafting content, the attackers have a high-chance of successfully compromising the individual within the organisation they're targeting.
Malicious campaigns using this technique to distribute 'FreeMilk' malware are known to have infiltrated several networks, including those of a Middle Eastern bank, European intellectual services firms, an international sporting organisation and 'individuals with indirect ties to a country in North East Asia'.
What is CEO fraud?
CEO fraud is a very specific type of phishing campaign which usually targets staff in the financial or human resources department of a business.
The target receives an email from the attacker which is disguised to look as if it comes from the CEO of the company or some other high level executive and - sometimes after a period of small talk to build up trust - it requests and urgent transfer of money to a particular account.
CEO fraud sees attackers posing as executives and sending multiple messages back and forth with victims.
Image: Trend Micro
Usually some sort of business reason is given such as the funds being required for a new contract or something similar. Of course, this message isn't from the CEO at all and the account doesn't belong to anyone within the company, but rather the attacker, who before the victim knows understands what is going on, has made off with a significant sum.
It's thought that at least $5 billion has been lost as a result of this particular form of phishing scam and law enforcement has warned that it continues to rise.
Other types of phishing attacks
While email still remains a large focus of attackers carrying out phishing campaigns, the world is very different to how it was when phishing first started. No longer is email the only means of targeting a victim as the rise of mobile devices, social media and more have provided attackers with a wider variety of vectors to use for attacking victims.
Social media phishing
With billions of people around the world using social media services such as Facebook, LinkedIn and Twitter, attackers are no longer restricted to use one means of sending messages to potential victims.
Some attacks are simple and easy to spot: a Twitter bot might send you a private message containing a shortened URL which leads to something bad such as malware or maybe even a fake request for payment details.
But there are other attacks which play a longer game. A common tactic used by phishers is to pose as a person - often an attractive women - using photos ripped from the internet, be it stock imagery or someone's public profile. Often these are just harvesting Facebook 'friends' for some future nefarious means and don't actually interact with the target.
However, sometimes plain old catfishing comes into play, with the attacker establishing a dialogue with the (often male) target - all while posing as a fake persona.
The 'Mia Ash' social media phishing campaign saw attackers operate a fake social media presence as if the fake persona was real.
Image: SecureWorks
After a certain amount of time - it could be hours, it could be months - the attacker might concoct a false story and ask the victim for details of some kind such as bank details, information, even login credentials, before disappearing into the ether with their gains.
These campaigns can be completely random, but some are specifically targeted with hackers running an entire online persona of a fake person across multiple social media sites in order to look like an authentic, real living person.
One campaign of this nature targeted individuals in organisations in the financial, oil and technology sectors with advanced social engineering based around a single, prolific social media persona that was absolutely fake.
Those behind 'Mia Ash' are thought to have been working on behalf of the Iranian government and tricked victims into handing over login credentials and private documents.
SMS and mobile phishing
The rise of mobile messaging services - Facebook Messenger and WhatsApp in particular - has provided phishers with a new method of attack, with the fact that smartphones are now in the pocket of the victims making them almost immediately accessible.
Attackers don't even need to use emails or instant messaging apps in order to meet the end goal of distributing malware or stealing credentials - the internet connected nature of the modern way phone means text messages are also an effective attack vector.
A SMS phishing - or Smishing - attack works in much the same way as an email attack, presenting the victim with a fraudulent offer or fake warning as a malicious incentive to click through to a malicious URL.
Text messages offer another attack vector to criminals.
Image: Action Fraud
The nature of text messaging means the smishing message is short and designed to grab the attention of the victim, often with the aim of panicking them into clicking on the phishing URL within. A common attack by smishers is to pose as a bank and fraudulently warn that the victim's account has been closed, had finances from it withdrawn or is otherwise compromised.
The truncated nature of the message often doesn't provide the victim with enough information to realise the message is fraudulent, especially when text messages don't contain tell-tale signs such as a sender address.
Once the victim has clicked on the link, the attack works in the same way as a regular phishing attack, with the victim duped into handing over their information and credentials to the perpetrator.
Cryptocurrency phishing
As the popularity - and value - of cryptocurrencies like Bitcoin, Monero and others grew, attackers wanted a piece of the pie. Some hackers use cryptojacking malware, which secretly harnesses the power of a compromised machine to mine for cryptocurrency.
However, unless the attacker has a large network of PCs, servers or IoT devices doing their bidding, making money from this kind of campaign can be an arduous task which involves waiting at least months to make a decent profit from the illicit activity.
Some attackers just don't have the patients to wait this amount of time and have therefore taken to using phishing to steal cryptocurrency directly from the wallets of legitimate owners.
Bitcoin and other cryptocurrencies are popular with cyber criminals.
Laremenko, Getty Images/iStockphoto
In a prominent example of cryptocurrency phishing, one criminal group conducts campaign which mimics the front of Ethereum wallet website MyEtherWallet and encourages users to enter their login details and private key.
Once this information has been gathered, an automatic script automatically create the fund transfer by pressing the buttons like a legitimate user would, all while the activity remains hidden from the user until it's too late.
The theft of cryptocurrency in phishing campaigns like this and other attacks is now worth millions.
How to spot a phishing attack
The whole point of attackers carrying out phishing attacks is to use deception in order to trick victims into compromising themselves, be it by installing malware onto the network, handing over login credentials or parting with financial data.
While at its heart phishing remains one of the most basic forms of cyber attack, the simple fact of the matter is that it works - and it's been working for over two decades.
While many in the information security sector might raise an eyebrow when it comes to the lack of sophistication of some phishing campaigns, it's easy to forget that there are billions of internet users - and everyday there are people who are only accessing the internet for the first time.
Large swathes of internet users therefore won't even be aware about the potential threat of phishing, let alone that they might be targeted by attackers using it - why would they even suspect that the message in their inbox isn't actually from the organisation or even friend it says it's from?
But while some phishing campaigns are so sophisticated and specially crafted that the message looks totally authentic, there are some key give-aways in less advanced campaigns which can make it obvious to spot an attempted attack.
Signs of phishing: Poor spelling and grammar
Many of the less professional phishing operators still make basic errors in their messages - notably when it comes to spelling and grammar.
Official messages from any major organisation are unlikely to contain bad spelling or grammar, let alone repeated instances throughout the body - so poorly written messages should act as an immediate warning that the message might not be legitimate.
It's common for attackers to use a service like Google Translate to translate the text from their own first language, but despite the popularity of these service they still struggles to make messages sound natural.
Shortened or odd URLs in phishing emails
It's very common for email phishing messages to coerce the victim into clicking through a link to a malicious of fake website designed for malicious purposes.
Many examples of phishing attacks will invite the victim to click through to an official-looking URL. However, if the user takes a second to examine the link more closely, they can hover the pointer over it and often find that while the text seems like the legitimate link, the actual web address is different.
In some instances, it can simply be a shortened URL, whereby the attackers hope the victim won't check the link at all and just click through. In other instances, attackers will take a minor variation on a legitimate web address and hope the user doesn't notice.
Attackers tried to take advantage of the Blizzard data breach by sending phishing emails claiming to be from Blizzard about account security.
Image: iStock
For example, a campaign once targeted online gamers after game developer Blizzard was hacked. Attackers spammed messages claiming that the victim had their World of Warcraft account compromised in the breach and asked them to click on a link and enter their details in order to secure it. The malicious link had only one minor difference to the real URL - the L in 'World' had been switched to a 1.
Ultimately, if you are suspicious of a URL in an email, hover over it to examine the landing page address and if it looks fake, don't click on it. And check that it is the correct URL and not one that looks very similar but slightly different to that which you'd usually expect.
A strange or mismatched sender address
You receive a message that looks to be from an official company account. The message warns you that there's been some strange activity using your account and urges you to click the link provided to verify your login details and the actions which have taken place.
The message looks legitimate, with good spelling and grammar, the correct formatting and the right company logo, address and even contact email address in the body of the message. But what about the sender address?
In many instances, the phisher can't fake a real address and just hope that readers don't check. Often the sender address will just be listed as a string of characters rather than as sent from an official source.
Another trick is to make the sender address almost look exactly like the company - for example, one campaign claiming to be from 'Microsoft's Security Team' urged customers to reply with personal details to ensure they weren't hacked. However, there isn't a division of Microsoft with that name - and it probably wouldn't be based in Uzbekistan, where the email was sent from.
Keep an eye on the sender address to ensure that the message is legitimately from who it says it is.
The message looks strange and too good to be true
Congratulations! You've just won the lottery/free airline tickets/a voucher to spend in our store - now just provide us with all of your personal information including your bank details to claim the prize. As is the case with many things in life, if it seems too good to be true, it probably is.
In many cases, phishing emails with the aim of distributing malware will be sent in a blank message containing an attachment - never clicking on mysterious, unsolicited attachment is a very good tactic when it comes to not falling victim.
Even if the message is more fleshed out and looks as if it came from someone within your organisation, if you think the message might not be legitimate, contact someone else in the company - over the phone or in person rather than over email if necessary - to ensure that they really did send it.
How to protect against phishing attacks
Training, training and more training. It might seem like a simple idea, but training is effective. Teaching staff what to look out for when it comes to a phishing email can go a long way to protecting your organisation from malicious attacks.
Exercises such as enabling staff to make errors - and crucially learn from them - in a protected sandbox environment or carrying out authorised penetration testing against employees can both be used to help alert users to potential threats and how to spot them.
At a technical level, disabling macros from being run on computers in your network can play a big part in protecting employees from attacks. Macros aren't designed to be malicious - they're designed to help users perform repetitive tasks with keyboard shortcuts.
Documents dropped by phishing attacks often ask the victim to enable Macros so as to enable the malicious payload to work.
Image: Digital Guardian
However, the same processes can be exploited by attackers in order to help them execute malicious code and drop malware payloads.
Most newer versions of Office automatically disable macros, but it's worth checking to ensure that this is the case for all the computers on your network - it can act as a major barrier to phishing emails attempting to deliver a malicious payload.
The future of phishing
It might have been around for almost twenty years, but phishing remains a threat for two reasons - it's simple to carry out - even by one-person operations - and it works, because there's still plenty of people on the internet who aren't aware of the threats they face. And even the most sophisticated users can be caught out from time to time.
For seasoned security personnel or technologically savvy people, it might seem strange that there are people out there who can easily fall for a 'You've won the lottery' or 'We're your bank, please enter your details here'.
But there are billions of people in the world who don't regularly use the internet or are just unaware that the internet is something which criminals might use to target them. Unfortunately, criminals are there looking to scam and deceive people and it's easiest to do it to people who are naive or overly trusting. And the low cost of phishing campaigns and the extremely low chances of scammers getting caught means it remains a very attractive option for fraudsters.
Because of this, phishing will continue as cyber criminals look to profit from stealing data and dropping malware in the laziest way possible. But it can be stopped and by knowing what to look for and by employing training when necessary, you can try to ensure that your organisation doesn't become a victim.
Source: Paper.li




















Phishing is a growing concern in today's digital world, and the information in this article is invaluable in helping people stay vigilant. Understanding the common signs of phishing attacks can significantly reduce the risk of falling victim to these scams. In addition to personal cybersecurity, businesses also need to ensure that they have proper legal protection against cyber threats. That's where business law services Robinson Markevitch & Parker come in. They can provide the necessary legal guidance and solutions to help protect your business from digital fraud and ensure you're compliant with cybersecurity regulations.
Understanding what phishing entails is crucial for safeguarding oneself from scam emails and other deceptive practices. Phishing involves fraudulent attempts to obtain sensitive information, such as passwords or financial details, by posing as a trustworthy entity. In the context of nursing professionals, this threat underscores the necessity of vigilance. Nurses, with the support of professionals like nurse attorneys and Nursing License Lawyers, play a crucial role in defending against deceptive practices. These dedicated legal experts, specializing in nursing licensure law, provide an aggressive defense for nurses facing challenges from the California Board of Registered Nursing, ensuring their protection against potential phishing threats and other legal pitfalls.
Oh boy, phishing. I've got a rather embarrassing tale about that. So, a few years back, my tech-enthusiast buddy, Max, dared me to identify and avoid a phishing attempt he'd stage. Being the ever-confident guy I am, I took up the challenge, only to fall flat on my face (not literally, though that would've been less painful). Trust professionals paulmankin.
So, here’s a quick rundown from my lesson learned the hard way:
Phishing, in a Nutshell: It's basically a type of scam where fraudsters try to trick you into sharing personal info, like passwords or credit card numbers, by pretending to be someone trustworthy. Think of it as someone trying to fish for your details using bait – hence the…