The system's use of GPS data could let hackers pinpoint who reports a positive diagnosis.
AS COUNTRIES AROUND the world rush to build smartphone apps that can help track the spread of Covid-19, privacy advocates have cautioned that those systems could, if implemented badly, result in a dangerous mix of health data and digital surveillance. India's new contact tracing app may serve as a lesson in those privacy pitfalls: Security researchers say it could reveal the location of Covid-19 patients not only to government authorities but to any hacker clever enough to exploit its flaws.
Independent security researcher Baptiste Robert published a blog post today sounding that warning about India’s Health Bridge app, or Aarogya Setu, created by the government’s National Informatics Centre. Robert found that one feature of the app, designed to let users check if there are infected people nearby, instead allows users to spoof their GPS location and learn how many people reported themselves as infected within any 500-meter radius. In areas that have relatively sparse reports of infections, Robert says hackers could even use a so-called triangulation attack to confirm the diagnosis of someone they suspect to be positive.
"The developers of this app didn’t think that someone malicious would be able to intercept its requests and modify them to get information on a specific area," says Robert, a French researcher known in part for finding security vulnerabilities in the Indian national ID system known as Aadhaar. "With triangulation, you can very closely see who is sick and who is not sick. They honestly didn’t consider this use of the app."
Security researchers like Robert have focused their attention on Aarogya Setu in part due to its sheer scale. The Indian government has declared the contact tracing app mandatory for many workers and it's already been downloaded more than 90 million times according to government officials.
Unlike many of the apps rolling out across Europe now and soon in the United States, Aarogya Setu traces potentially infected people's movements via GPS rather than Bluetooth data alone. It may represent a cautionary tale about how flawed implementations of contact tracing apps—particularly those that rely on location data—can lead to serious leaks of sensitive medical information. "I expect many of the contact tracing apps to have these types of issues, and I think particularly the ones that rely on GPS are going to be more privacy invasive," says Ashkan Soltani, a former Federal Trade Commission lead technologist who reviewed Robert's findings and analyzed other contact tracing apps. "When you tie it to something like health status, it’s not surprising that these types of inferences can be made."
Robert first recognized Aarogya Setu's privacy problem when he analyzed a feature that checks for reports of infected people within a certain radius. He found that by mimicking those requests from his laptop, he could simply spoof his location, altering the queries to ask for the number of infected people in a 500-meter radius around any latitude and longitude.
That GPS spoofing possibility is troubling enough on its own. If someone lives in a remote area, they could easily be identified as Covid-19 positive. But Robert suggests that the bug could also be used to carry out a technique known as triangulation or trilateration, finding the reported Covid-19 status of someone in a far more targeted location.
"The intended use of the apps is privacy invasive."
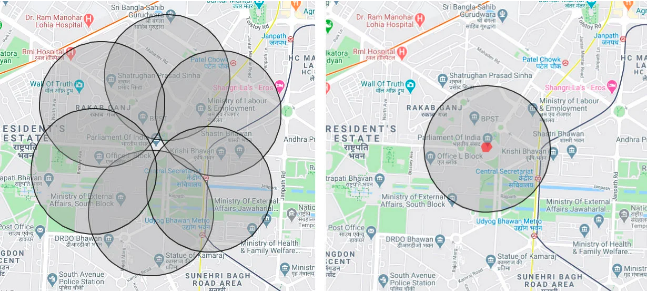
If a hacker suspects that someone has Covid-19, they could check a series of overlapping 500-meter circular areas around their target, carefully placing the centers of those circles so that they don’t cover their target’s home, but so that the edges of the circles create a boundary around it. If each of those 500-meter-radius areas contains zero infected people, the hacker would then draw new circle, this time positioning its center over the person’s home. If the count of sick people goes up by one, the hacker can deduce that an infected person is in that narrowly defined location. “If I want to know if the people in a house are sick, I can draw a boundary around it and the application will give me the result,” Robert says. Most Popular
A sample triangulation attack targeting the Indian Parliament: If the attacker can measure all the areas around a target, creating a tight boundary, and determine there are no infected people, (as shown on the left) they can then count the number of infected people at the target location with much more precision (shown on the right). The red hexagon represents the more precise area where the attacker can check for a reported Covid-19 case.
The trick has some serious limitations. Though Robert says it could be used to determine a Covid-19 infected person's location down just a few meters in each dimension, that would depend largely on the precision of the app's measurements. Robert says he didn't fully test the technique, in part to avoid privacy violations. "I did the minimum to validate it was working," he says.
The triangulation would also be most effective when a suspected Covid-19 positive person is the only reported case in roughly a kilometer radius. That last condition isn't quite as unlikely as it may sound, at least for now; despite India's high population density, Robert checked 500-meter-radius areas in central areas of New Delhi and found that in most cases only one or two people had reported as Covid-19 positive. Rural locales may be far easier targets.
Neither India's Computer Emergency Response Team nor its National Informatics Centre responded to WIRED's request for comment. But a Twitter account for the developer group behind the app posted a statement, which claimed that "no personal information of any user has been proven to be at risk," and that "no data or security breach has been identified." The statement also seems to argue that a user's ability to spoof a different location is a feature rather than a bug: "The user can change the latitude/longitude to get the data for multiple locations."
The statement doesn't address the potential for targeting users via triangulation, but does state that a web application firewall limits the frequency of requests a user can make from the app. But Robert points out that the triangulation technique could require fewer than 10 location reads in succession, which he found he could easily carry out in his testing. With more measurements, perhaps from multiple accounts to defeat the app’s firewall, a hacker could determine a target’s Covid-19 positive status with more certainty. Former FTC technologist Soltani argues that even given the triangulation vulnerability, India's app makes more fundamental privacy compromises due to its GPS location-tracking features. "This is the intended use: You get to see where people are infected, which is what we would consider a privacy violation but also a public health need," Soltani says. "The intended use of the apps is privacy invasive."
Location has been a particular sticking point in debates between developers focused on contact tracing apps and privacy advocates. Since traces of the novel coronavirus left on surfaces can infect people—what's known as "environmental transmission"—some app developers have argued that measuring proximity between users with Bluetooth alone isn't enough to catch all exposure possibilities. But location tracking, even when it's done more securely than in the Aarogya Setu case, can allow government authorities to learn people's movements, potentially revealing sensitive activities that range from extramarital affairs to political opposition groups. Even complex cryptographic schemes can't perfectly protect against the abuse of those location-tracking systems.
But Robert argues that beyond the deeper questions of privacy and public health tradeoffs in contact tracing apps, Aarogya Setu's flaws shows that developers in some cases aren't even building the apps with basic security measures. "What I found was super easy to do, and I don’t understand why no one took a look before me," Robert says. "We need new tools to fight Covid-19. We’re in a crisis. But we still need to take care to build with security and privacy in mind."
Source: paper.li




Comments