Fake ransomware decryptor double-encrypts desperate victims' files
- The Tech Platform

- Jun 8, 2020
- 2 min read
A fake decryptor for the STOP Djvu Ransomware is being distributed that lures already desperate people with the promise of free decryption. Instead of getting their files back for free, they are infected with another ransomware that makes their situation even worse.
While ransomware operations such as Maze, REvil, Netwalker, and DoppelPaymer get wide media attention due to their high worth victims, another ransomware called STOP Djvu is infecting more people then all of them combined on a daily basis.
With over 600 submissions a day to the ID-Ransomware ransomware identification service, STOP ransomware is the most actively distributed ransomware over the past year.
STOP Djvu ransomware submissions to ID-Ransomware
Emsisoft and Michael Gillespie had previously released a decryptor for older STOP Djvu variants, but newer variants cannot be decrypted for free.
If the ransomware is so common, you may be wondering why it doesn't get much attention?
The lack of attention is simply because the ransomware mostly affects home users infected through adware bundles pretending to be software cracks.
While downloading and installing cracks is not excusable, many of those who are infected simply cannot afford to pay a $500 ransom for a decryptor.
Double-encrypting someone's data with a second ransomware is just kicking someone while they are already down.
Zorab double-encrypts a victim's data
Unfortunately, this is what a new ransomware called Zorab discovered by Michael Gillespie is doing.
The creators of the Zorab ransomware have released a fake STOP Djvu decryptor that does not recover any files for free but instead encrypts all of the victim's already encrypted data with another ransomware.
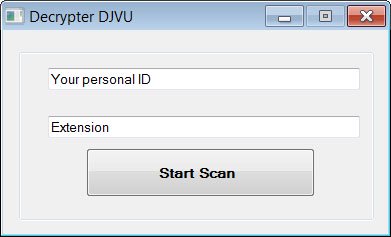
Fake STOP Djvu decryptor
When a desperate user enters their information in the phony decryptor and clicks on 'Start Scan,' the program will extract another executable called crab.exe and saves it to the %Temp% folder.
Extracting and executing the crab.exe program
Crab.exe is another ransomware called Zorab, which will begin to encrypt the data on the computer. When encrypting files, the ransomware will append the .ZRB extension to the file's name.
Zorab encrypted files
The ransomware will also create ransom notes named '--DECRYPT--ZORAB.txt.ZRB' in each folder that a file is encrypted. This note contains instructions on how to contact the ransomware operators for payment instructions.
Zorab ransom note
This ransomware is currently being analyzed, and users should not pay the ransom until it is confirmed no weakness can be used to recover Zorab encrypted files for free.
IOCs
Hashes:
Fake decryptor: 1abf41be04801cfc3478502127abc47c2d84253ab659d576e5c02cc0b716c782
Associated files:
Decryptor Djvu mlagham.exe
%Temp%crab.exe
--DECRYPT--ZORAB.txt.ZRBRansom note text:
—+-= ZORAB =-+—
Attention! Attention! Attention!
Your documents, photos, databases and other important files are encrypted and have the extension: .ZRB
Don't worry, you can return all your files!
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
if you want to decrypt your files
The only method of recovering files is to purchase decrypt tool
This tool will decrypt all your encrypted files.
To get this software you need write on our e-mail: zorab28@protonmail.com
What guarantees do we give to you?
Its just a business. We absolutely do not care about you and your deals, except getting benefits.
You can send 2 your encrypted file from your PC and we decrypt it for free.
+--Warning--+
DONT try to change files by yourself, DONT use any third party software for restoring your data
Your personal id: xxx
Associated emails:
Source: Paper.li













Comments