Configure Search And Investigation On The Security And Compliance Center On SharePoint Office 365
- Manpreet Singh

- Aug 15, 2019
- 2 min read
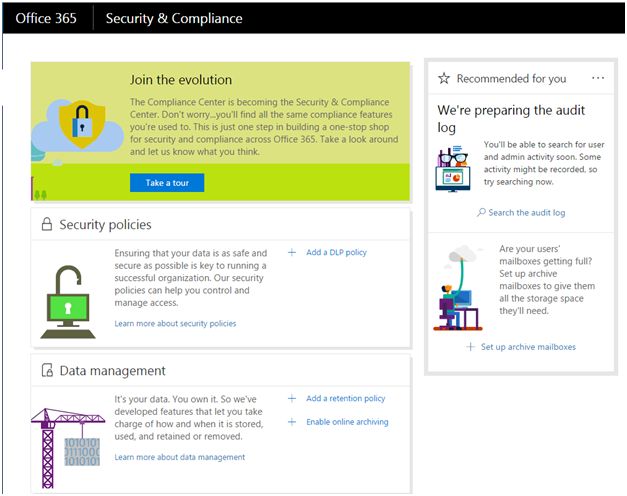
You can configure the search policy and view the usage logs of your users present in Office 365, using this portal.
If you are a tenant administrator, open your Office portal and click “Security & Compliance.”
You will reach your security and compliance center.
We have here,
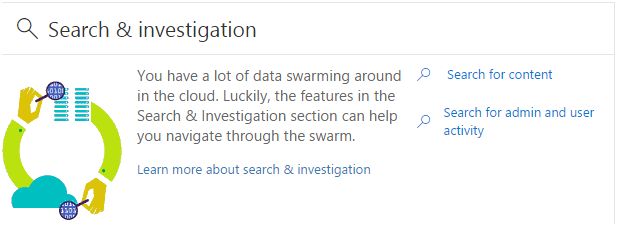
Search & Investigation
Search for content
Content Search is unimaginable in Cloud. It has surpassed the crawling technologies and the extensive search is just awesome in Office 365.
Here, we can configure what we want to search, when we try to search the content.
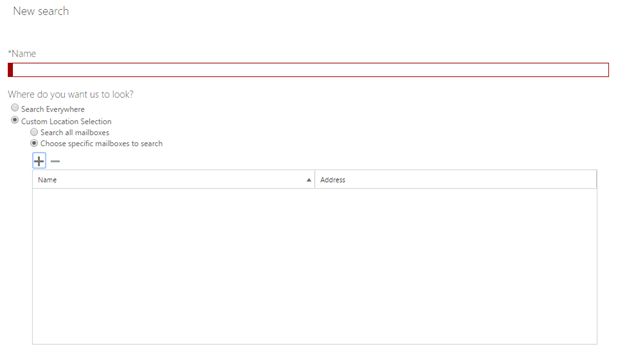
Click the “+” symbol to configure a new search.
Provide a name to your search.
Mailboxes You can specify if you want the search to find the content in all the mail boxes or a specific user’s mail box.
If you choose specific, click on the “+” icon and specify the user as per the screenshot, given below:
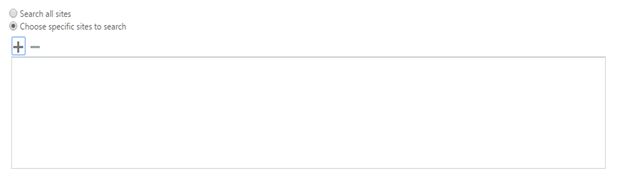
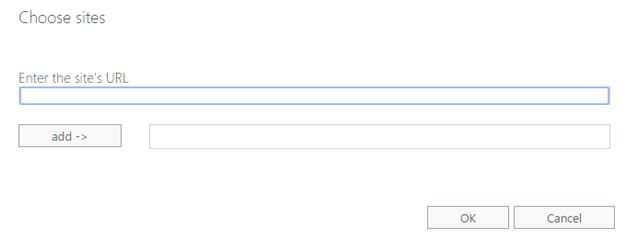
Sites Similarly, you can choose all the sites in the tenant to be searched or the specific sites.
If you choose specific, click the “+” icon and specify the sites shown in the screenshot, given below:
Public Folders Similarly, you choose the public folders, and if they are required to be included in the search or not.
Keywords Specify the keywords here, which you want to search.
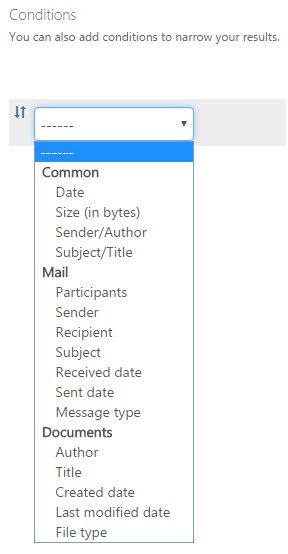
Conditions You can also choose the conditions to narrow down your search results.
Once your query is ready, hit search and the desired results will be fetched by the search center.
It will be a quick and direct, to-the-point request.
Investigation
Why do we need an investigation?
We need to know what the users on our tenant are doing, what are they viewing and all the other activities. It is very important for an organization to be able to track down its user’s movements.
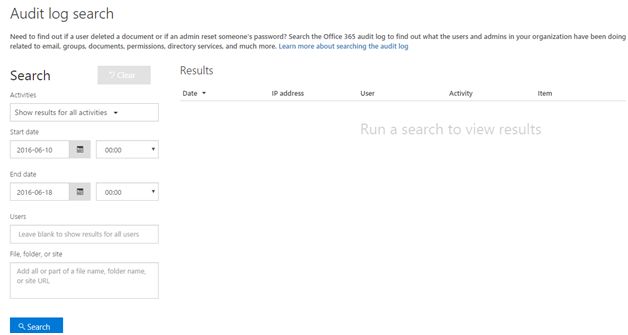
Click on “Search for Admin & User Activity”.
Here, you can search the users' or admin activities and view them with a few clicks.
Let’s see how:
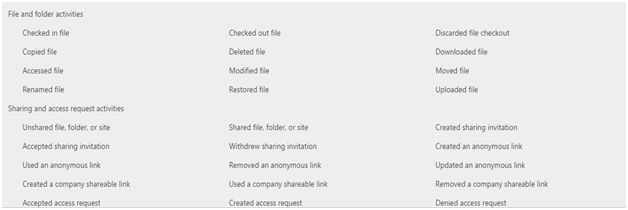
Activities You can either choose all the users' activity or you can use the categories as shown below:
Dates Use dates to search the activity between the intervals of time.
Users You can either specify all the users and search them all or any particular user. Isn’t it great!
File, Folder or site If you want the activity log to be pulled on the specific file or a folder or a site, you can configure and fetch the results.
Here, you will have complete control over the important documents, control over the users and many other things. This is something like the top secret section of your organization.
Here, in this article, we saw two important configurations under the search & investigation on security & compliance, which were to search the content and investigation, which are very important for our organization. There is always more to learn. Keep reading and learning.














Comments