Antivirus firm Avast sold user data via 'Jumpshot' to Pepsi, Google, Microsoft — REPORT
- The Tech Platform

- Jan 28, 2020
- 2 min read
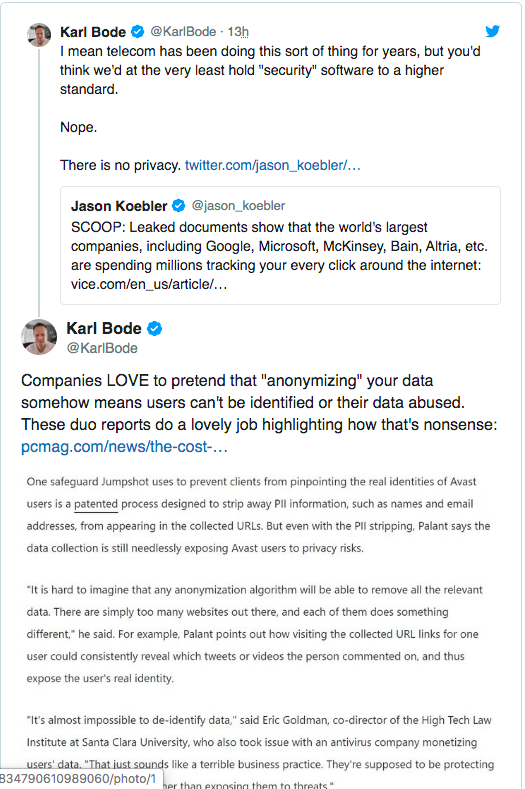
Documents show that the antivirus company Avast has been selling its users' internet browsing data, through a subsidiary named Jumpshot, to clients that include Pepsi, Google, and Microsoft, reports Motherboard. The report is the result of a joint investigation between the VICE News site and PC Mag.
“An Avast antivirus subsidiary sells 'Every search. Every click. Every buy. On every site,'” and clients of that data broker firm, Jumpstart, have included Home Depot, Google, Microsoft, Pepsi, and McKinsey,” Joseph Cox at Vice/Motherboard.
“An antivirus program used by hundreds of millions of people around the world is selling highly sensitive web browsing data to many of the world's biggest companies,” the joint investigation with VICE Motherboard and PCMag found.
Excerpt:
The documents, from a subsidiary of the antivirus giant Avast called Jumpshot, shine new light on the secretive sale and supply chain of peoples' internet browsing histories. They show that the Avast antivirus program installed on a person's computer collects data, and that Jumpshot repackages it into various different products that are then sold to many of the largest companies in the world. Some past, present, and potential clients include Google, Yelp, Microsoft, McKinsey, Pepsi, Sephora, Home Depot, Condé Nast, Intuit, and many others. Some clients paid millions of dollars for products that include a so-called "All Clicks Feed," which can track user behavior, clicks, and movement across websites in highly precise detail.
Avast claims to have more than 435 million active users per month, and Jumpshot says it has data from 100 million devices. Avast collects data from users that opt-in and then provides that to Jumpshot, but multiple Avast users told Motherboard they were not aware Avast sold browsing data, raising questions about how informed that consent is.
The data obtained by Motherboard and PCMag includes Google searches, lookups of locations and GPS coordinates on Google Maps, people visiting companies' LinkedIn pages, particular YouTube videos, and people visiting porn websites. It is possible to determine from the collected data what date and time the anonymized user visited YouPorn and PornHub, and in some cases what search term they entered into the porn site and which specific video they watched.
SOURCE: Paper.li


















Comments